3-minute read
If you want proof that data privacy needs to be included in M&A due diligence, look no further than the proposed $123 million GDPR fine against Marriott International. The UK Information Commissioner’s Office (ICO) based the fine on a data breach at Starwood Hotels before Marriott acquired them, even though the breach was not discovered until after the acquisition.
As we explored in recent Insights, data privacy compliance is becoming a key issue in mergers and acquisitions for both acquirers and sellers. Acquirers are incorporating data privacy inquiries into their due diligence processes to avoid taking on privacy-related liabilities, and target companies must be prepared to respond to acquirers’ questions and address any gaps. Once the merger or acquisition closes, additional steps may be needed to prepare the combined entity for GDPR, CCPA, or other data privacy regulations that apply to it.
Data privacy and application rationalization
To realize the benefits of most M&A deals, the post-merger organization must determine the best approach to eliminating redundancies in business processes and IT systems. This rationalization can take one of two general forms. Either the post-merger company will maintain all or most of the acquirer’s application portfolio, possibly incorporating some applications from the target, or a new portfolio will be built featuring best-of-breed applications from both organizations.
Regardless of which approach is chosen, rationalization requires special considerations with regard to data privacy, including:
- Analysis of the original use of personal data compared to post-merger use
- Revised system inventory of applications that house personal data and updated data mapping
- Updated business processes to handle data subject requests (DSRs), such as requests for access, portability, or deletion
Data privacy and system integration
As we discussed in our earlier Insight regarding data privacy concerns for acquirers, the target’s data lifecycle and ability to respond to data subject requests should be evaluated before an offer is made. Ideally, plans for integrating data systems should be in place before the deal closes.
When we work with clients to build a data privacy readiness program from the ground up, our methodology begins with understanding the business processes that involve personal data and moves through an analysis of the data architecture:
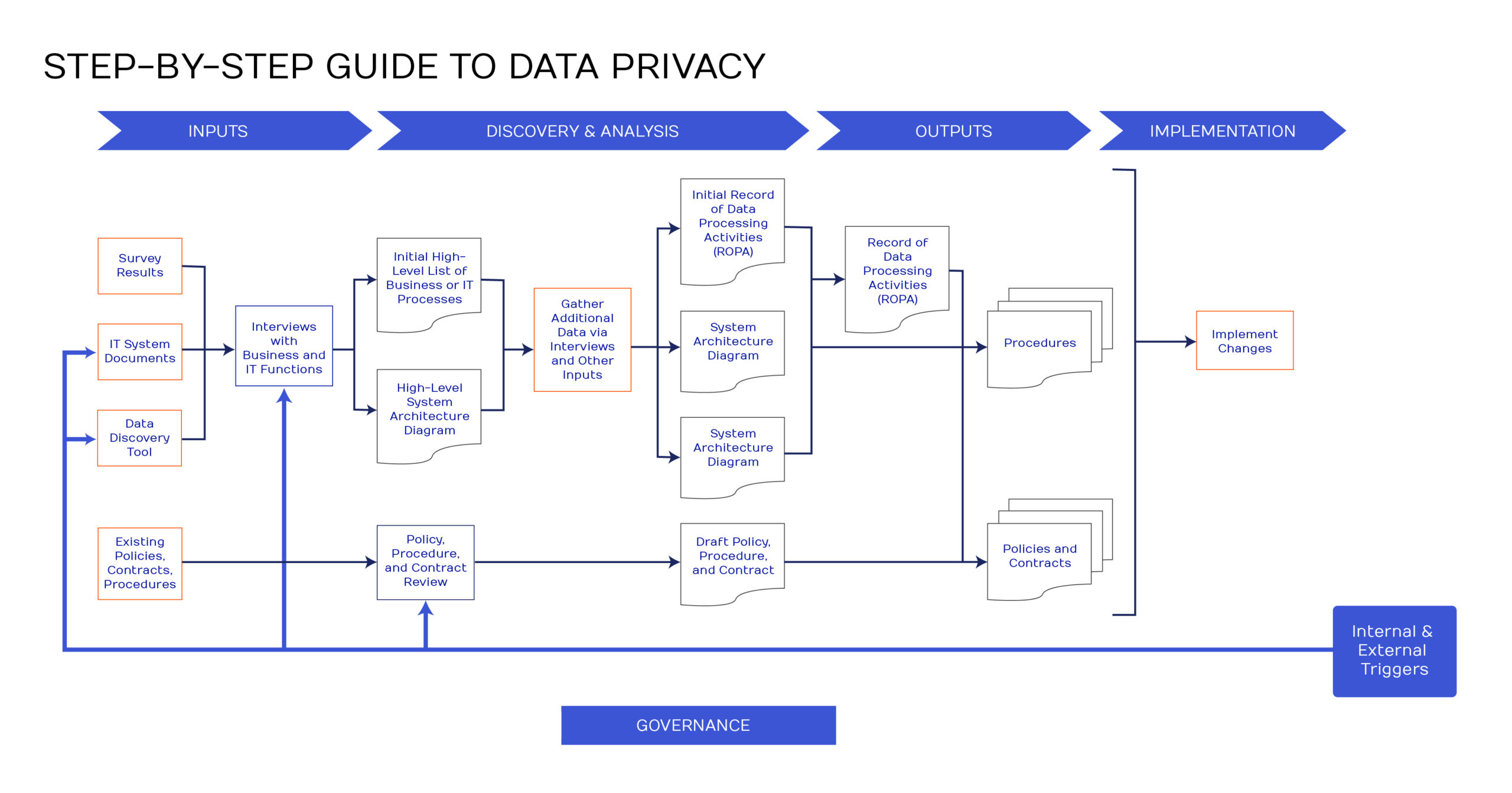
How much of this process will be needed after the merger depends on the compliance status of both companies at the time of the deal. If both the acquirer and the seller followed a process similar to the one above before the deal, the post-merger organization should have the inputs it needs to create updated system architecture diagrams, data flow diagrams, and records of processing activities (ROPAs), which can then inform updates to policies, procedures, and contracts. If either party had gaps in their preparedness processes, some additional inputs may be required to build the understanding of the post-merger data lifecycle that is needed to achieve data privacy readiness.
In any merger or acquisition, data privacy should play a key role in both the acquirer’s due diligence processes and the seller’s preparatory strategies. For the combined entity to be ready for GDPR, CCPA, and/or other regulations, it will need to address data privacy readiness after the deal is complete. Fortunately, if both parties were prepared before the merger, much of the background work may already have been done. The new company will have a solid basis for moving forward not only in preparing for existing regulations, but also for building a firm foundation that can adapt to future requirements.